Featured articles
- Latest News
Researchers have uncovered a serious vulnerability in Anthropic’s Claude Code sandbox that could allow attackers to bypass network restrictions and ...
- AI Security
Prompt injection is a high-priority cybersecurity threat where attackers insert malicious instructions
By
- Latest News
Microsoft has revealed details of a sophisticated cloud-focused attack campaign where hackers
By
- AI Security
Hermes Agent is an open-source autonomous AI agent by Nous Research that
By
- Defensive Security
The Open Systems Interconnection (OSI) model is a conceptual model created by the International Organization for Standardization that enables diverse communication systems to communicate using ...
By
- Defensive Security
In today’s world, where technology is part of everyday life, the word “cybersecurity” is often thrown around and can be overstated. Authentication is an incredibly ...
By
- Defensive Security
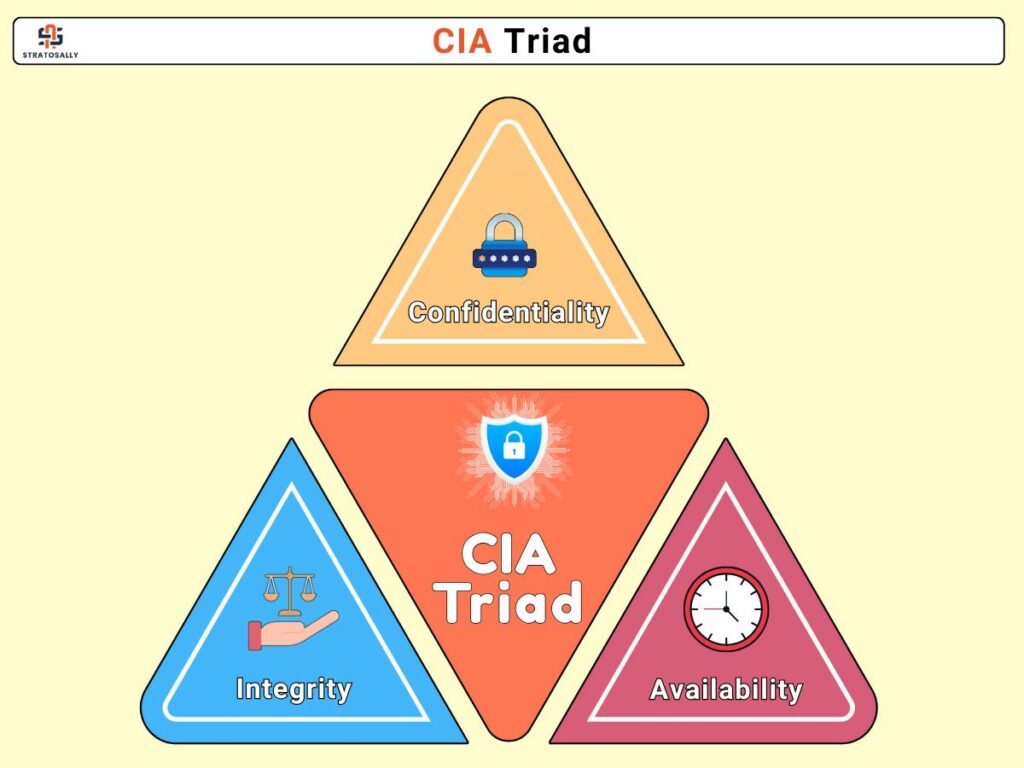
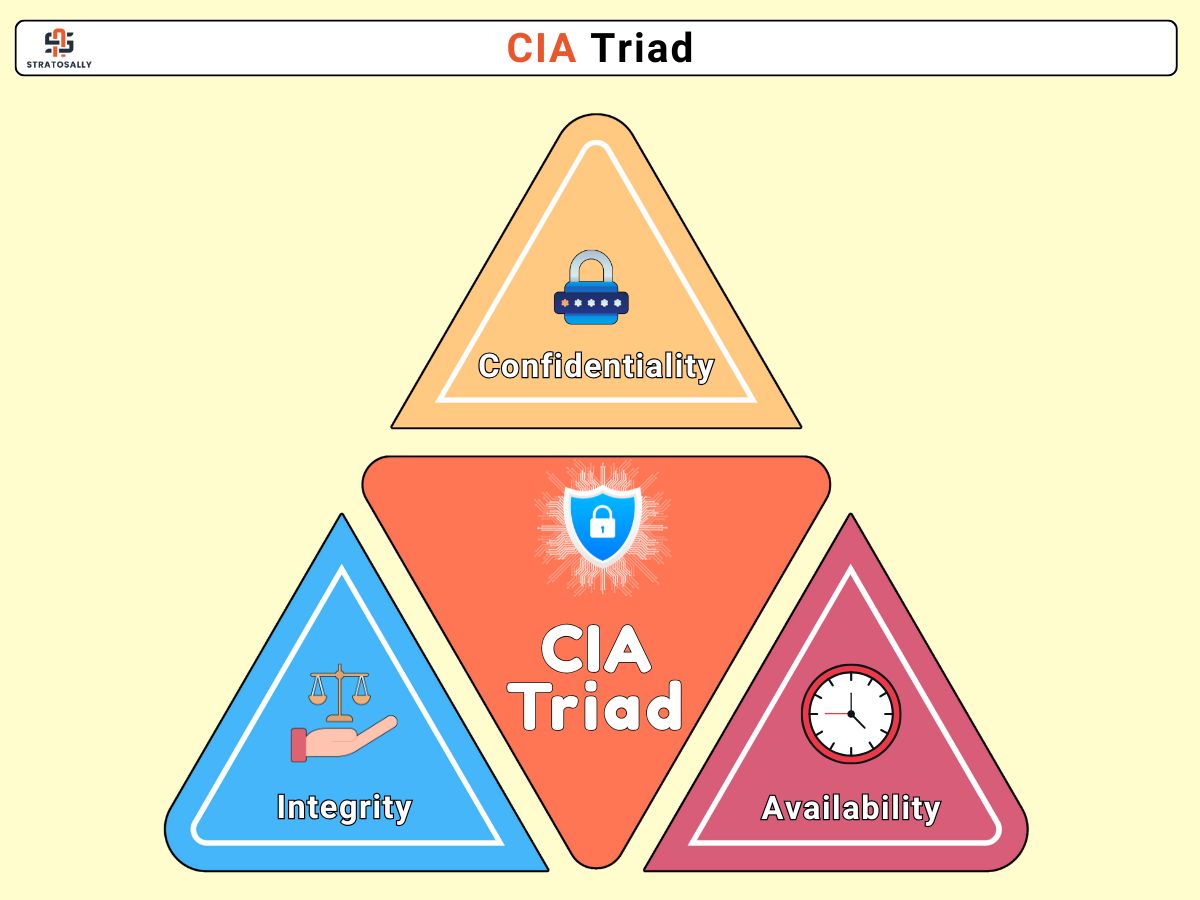
In the subject of information security, the CIA Triad provides a key paradigm for developing and assessing secure systems. This model outlines the fundamental goals ...
By
- Defensive Security
Imagine this: You’re at your favorite coffee shop, having a latte and browsing the internet. You have no idea that the public Wi-Fi you just ...
By
By
community
Join the community to
Stay Updated
with the Latest Cybersecurity
Trends
Subscribe to our newsletter for exclusive insights, industry news,
and valuable resources.
latest in offensive security
AI-assisted “vibe coding” is transforming development velocity — but it’s also shipping silent vulnerabilities at scale. Here’s what’s at stake ...
Introduction In the ever-evolving world of cybersecurity, intelligence gathering is the pillar
By
**Note: The content in this article is only for educational purposes and
By

more related posts
- Latest News
Attackers breached DigiCert’s support environment using a disguised malicious file, accessed certificate-related data, and issued legitimate code-signing certificates that were later used to sign malware, turning ...
By
- Latest News
A coordinated international operation led to 276 arrests, the dismantling of nine scam centers, and the seizure of over $701 million tied to large-scale cryptocurrency ...
By
- Latest News
A newly discovered Linux kernel flaw, CVE-2026-31431 (Copy Fail), allows any regular user to gain full root access. Even more concerning, the exploit is simple, ...
By
- Latest News
It’s one of those moments where the risk doesn’t come from what AI can do, but from how it’s built.A critical vulnerability has been uncovered ...
By
- Latest News
Sometimes, the tools designed to find weaknesses end up revealing one of their own, and that’s exactly what’s unfolding with Nessus Agent on Windows. A ...
By
- Latest News
Hackers are now switching their style. It doesn’t begin with a suspicious email anymore. No strange links, no obvious red flags. Just a message on ...
By
- Soft Skills
You finally got the job, the one you worked for, stayed up late for, and quietly hoped would change everything. It feels like you’ve made ...
By
- Latest News
What was meant to be one of the most tightly controlled AI systems in the world has suddenly found itself at the center of an ...
By