- Defensive Security
In today’s world, where technology is part of everyday life, the word “cybersecurity” is often thrown around and can be overstated. Authentication is an incredibly ...
By
- Latest News
A serious security hole in Google Chrome, called CVE-2025-2783, was recently exploited by a hacking group named TaxOff to quietly install a backdoor malware known ...
By
- Latest News
A newly discovered ransomware strain, known as “Anubis,” is turning heads in the cybersecurity world. Unlike conventional ransomware that solely encrypts data, Anubis poses a ...
By
- Latest News
A novel threat campaign is leveraging a design flaw in the Discord invitation system to distribute AsyncRAT and a customized version of Skuld Stealer, both ...
By
- Latest News
ConnectWise is updating how it signs and configures tools like ScreenConnect and Automate, following recent concerns over how older versions handled setup data. A researcher ...
By
- Latest News
INTERPOL and partner nations have wrapped up a sweeping operation, dubbed Operation Secure, aimed at cracking down on data theft tools online. Between January and ...
By
- Latest News
On June 5, 2025, GreyNoise, security analyst observed a sharp increase in attempts to access at Apache Tomcat Manager systems, with much of traffic traced ...
By
- Defensive Security
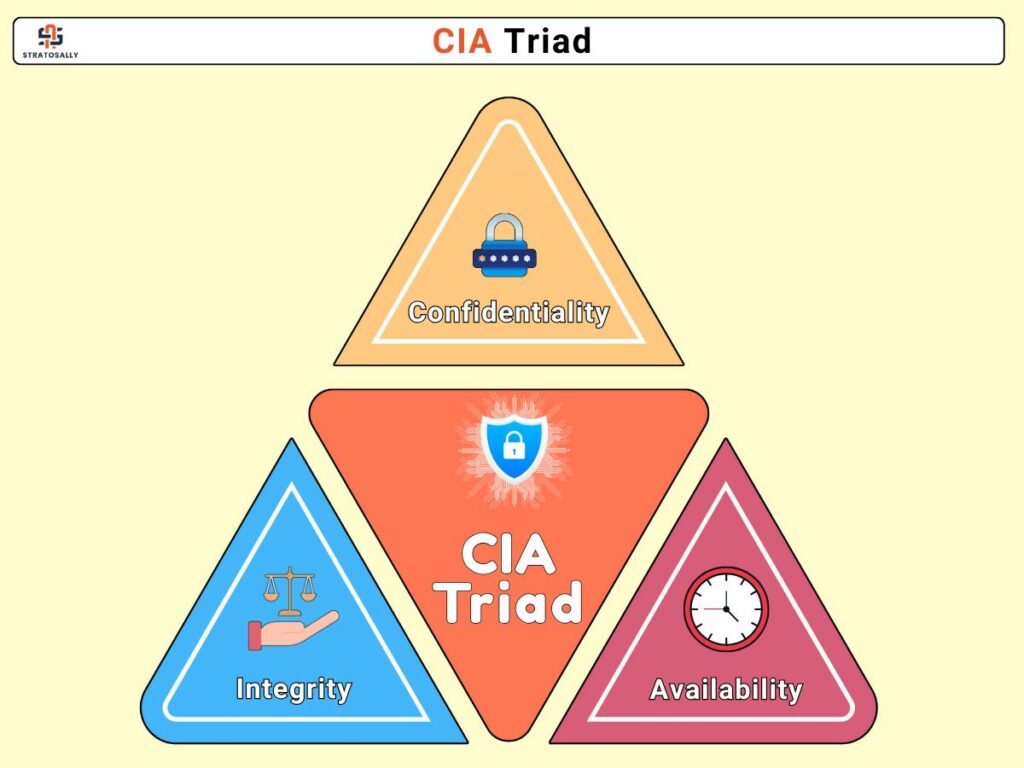
In the subject of information security, the CIA Triad provides a key paradigm for developing and assessing secure systems. This model outlines the fundamental goals ...
By
- Latest News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a fresh warning after adding two high-risk vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, ...
By